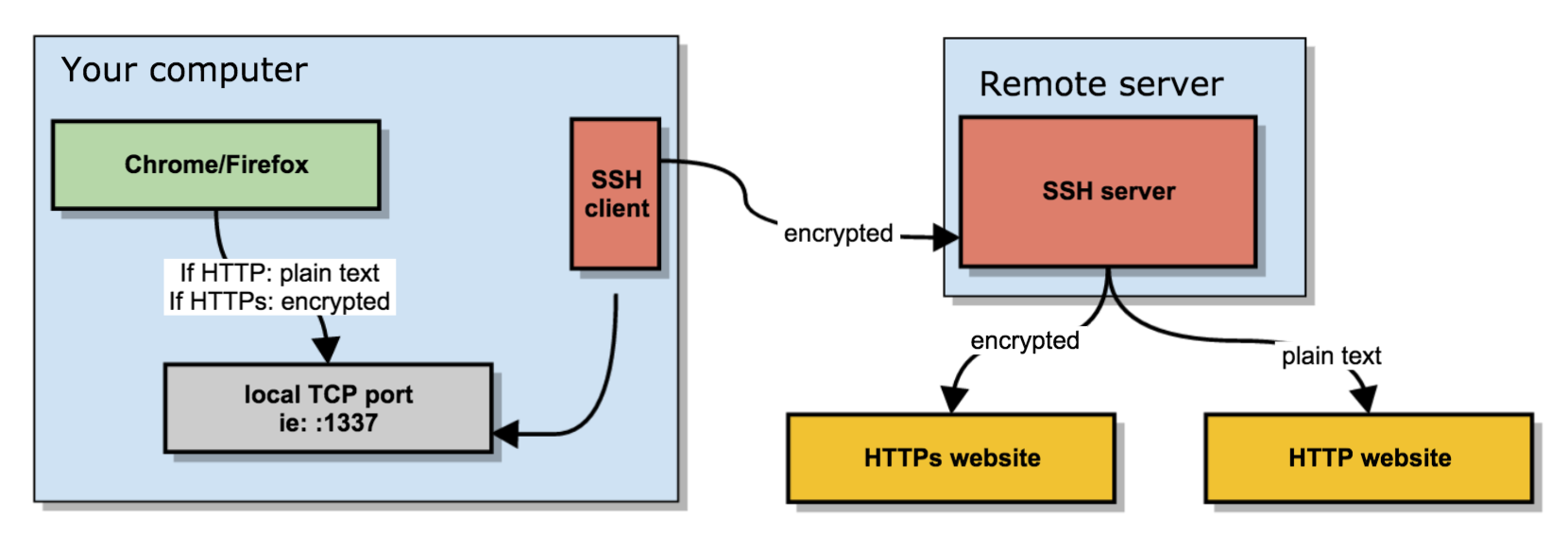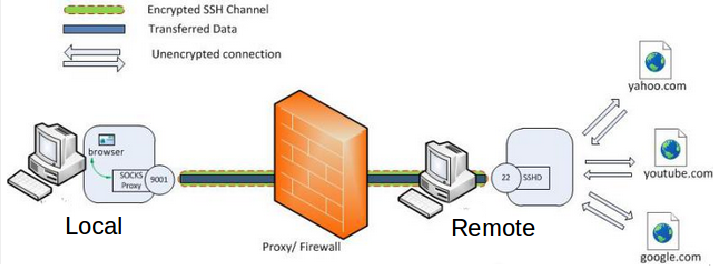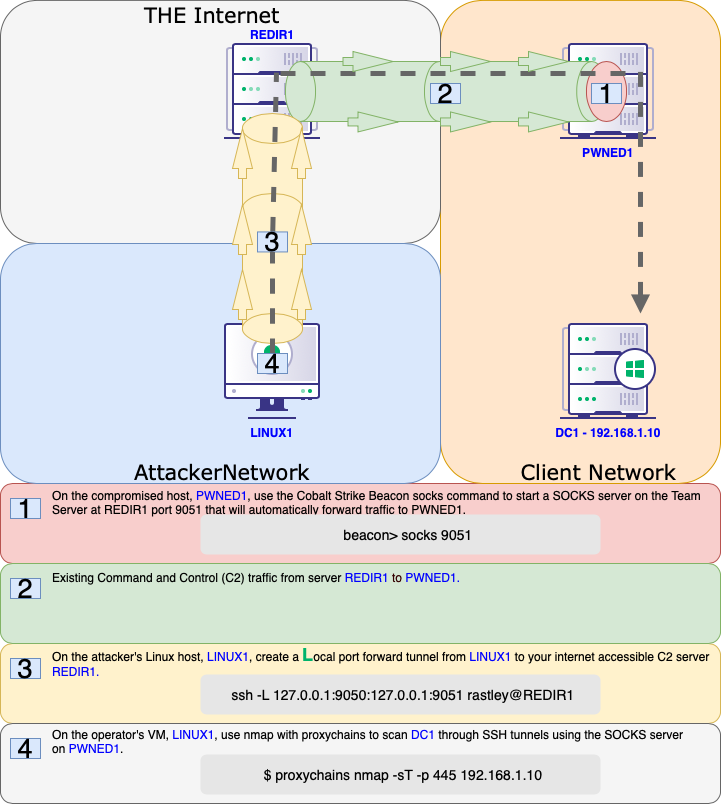
Offensive Security Guide to SSH Tunnels and Proxies | by Russel Van Tuyl | Posts By SpecterOps Team Members

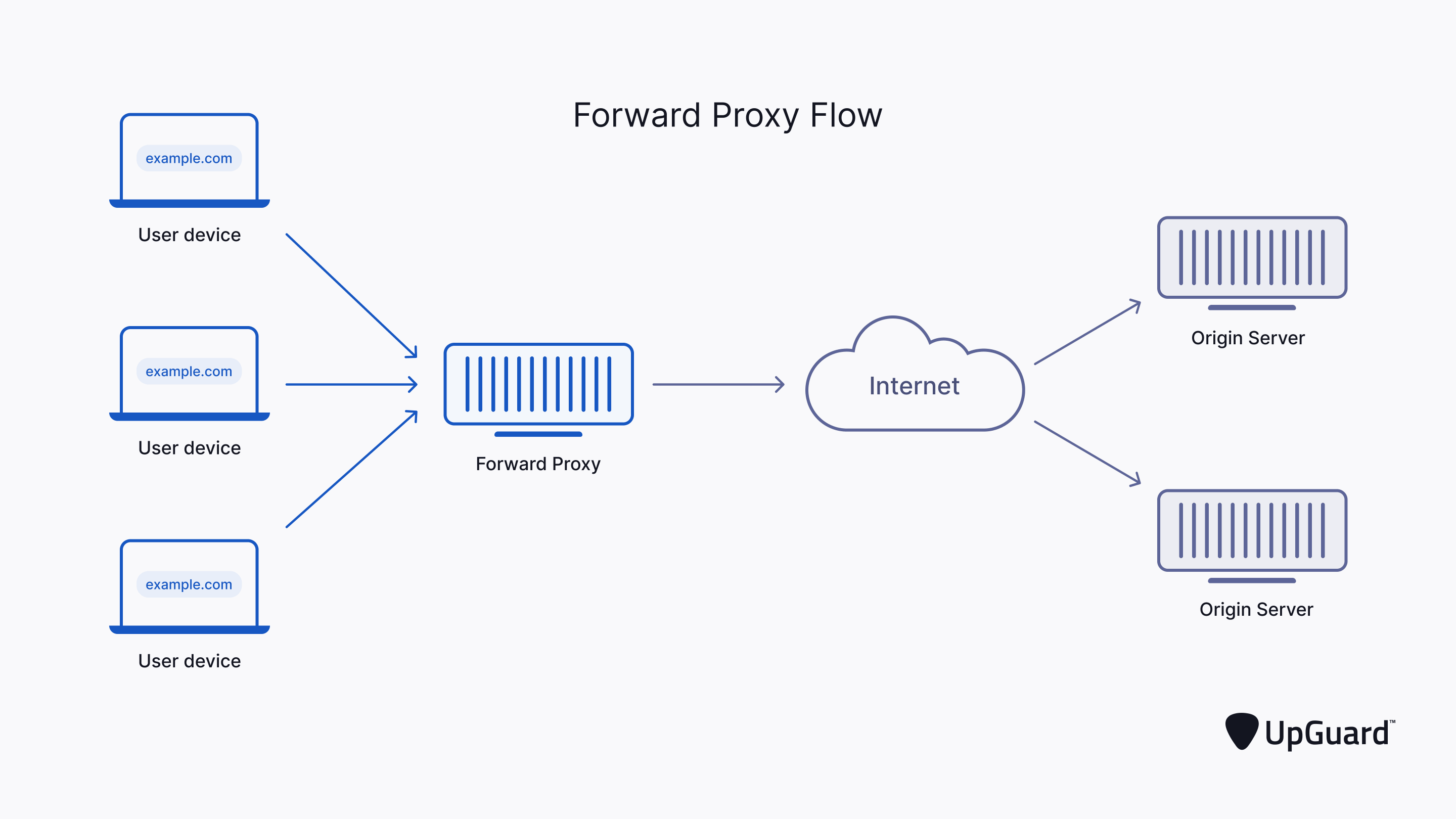
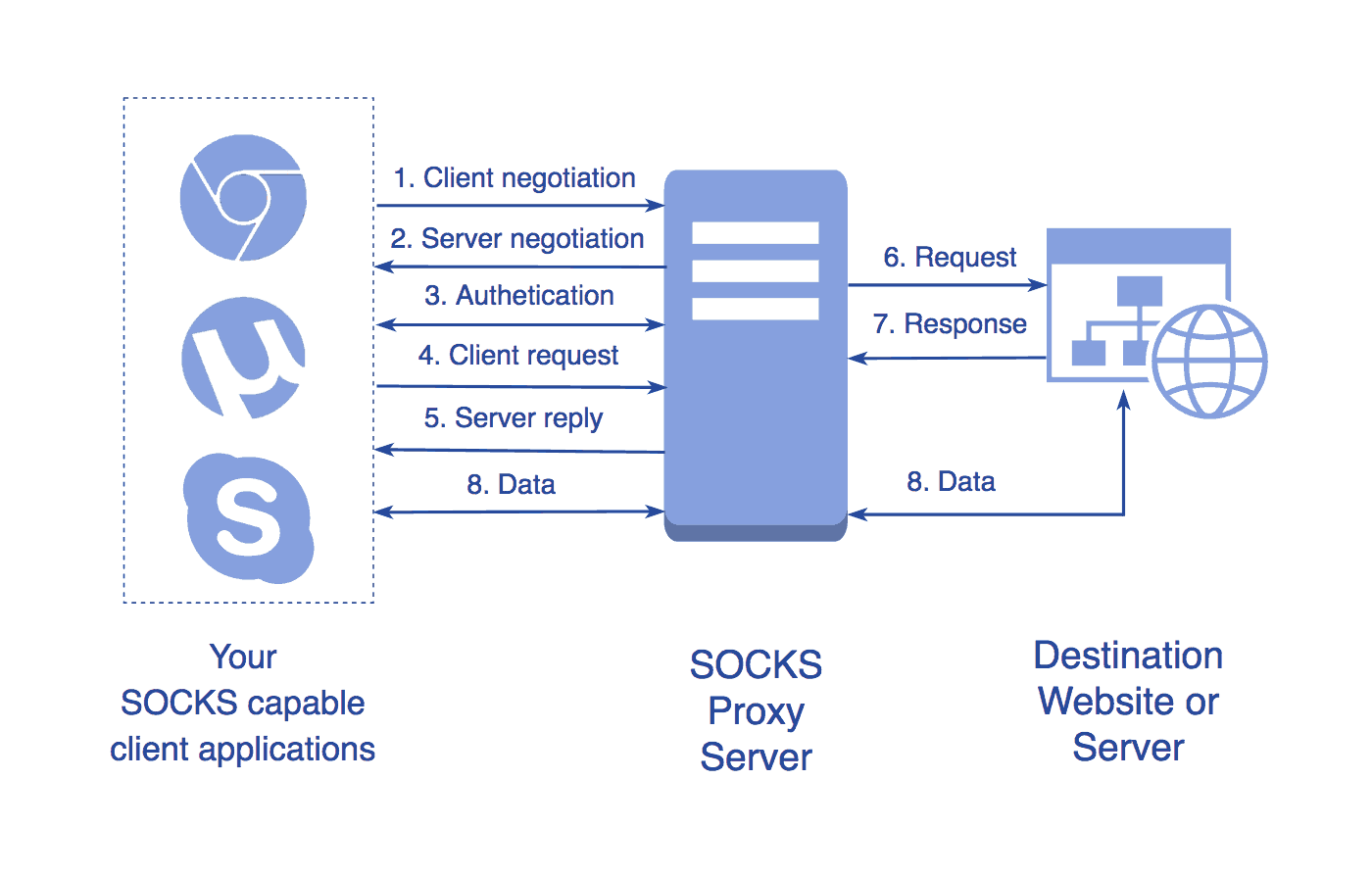
A socks proxy server that sends each request to a random proxy. Also a web proxy that uses a random user-agent for each request and then forwards it to the socks proxy. :

Core Impact Agent and Proxychain Tunneling – Cyber Security Architect | Red/Blue Teaming | Exploit/Malware Analysis
Proxy Windows Tooling via SOCKS. Leveraging SOCKS to proxy tools from a… | by Nick Powers | Posts By SpecterOps Team Members